Hundreds of crypto wallets were drained across multiple blockchains following a supply chain attack on Trust Wallet’s Chrome browser extension, according to on-chain investigator ZachXBT.
While early reports described the cause as unclear, subsequent analysis has linked the losses to a compromised extension release distributed around Christmas 2025.
Trojanized Chrome Extension Identified as Root Cause
Investigations now point to Trust Wallet Chrome extension version 2.68 as the attack vector. The incident was not a user error or phishing campaign, but a developer-side supply chain compromise.
Attackers reportedly gained access to Trust Wallet’s Developer GitHub secrets and its Chrome Web Store (CWS) API key, enabling them to upload a malicious, trojanized version of the extension directly to the official Chrome store.
This backdoored release contained injected JavaScript code designed to capture wallet mnemonic phrases as users entered them. Once exposed, private keys could be used to drain funds across every blockchain supported by the wallet.
Wallet Drains Spread Across Nearly 20 Chains
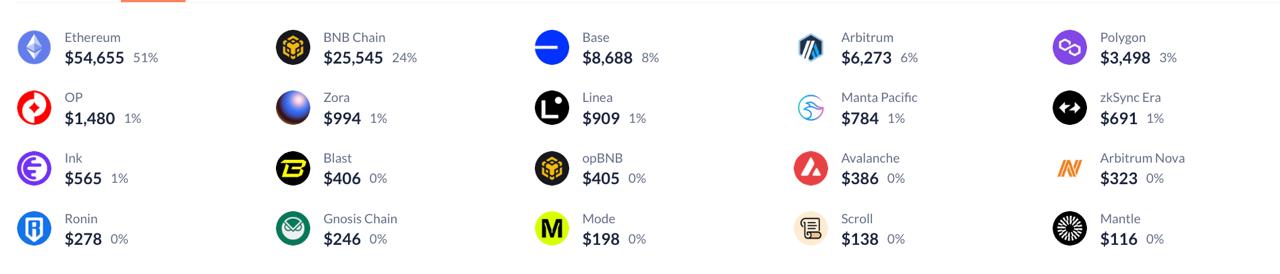
Because the compromised extension handled multiple networks, attackers were able to move quickly across ecosystems. Funds have been traced across nearly 20 EVM-compatible chains, including:
- Ethereum
- BNB Chain
- Base
- Arbitrum
- Polygon
Because mnemonic phrases were compromised, affected users also saw assets drained on non-EVM chains, including Bitcoin and Solana, even though the initial exploit occurred via an EVM-focused extension.
Total losses are estimated between $6 million and $7 million, with most individual wallet drains under $2,000, suggesting a broad, automated sweep rather than targeted high-value attacks.
Who Was Affected and Who Wasn’t
The incident was limited strictly to users running Trust Wallet Chrome extension v2.68. Users who relied solely on mobile versions of Trust Wallet were not impacted.
Trust Wallet has since released version 2.69, which removes the malicious code and closes the compromised access points.
Urgent Steps for Users
Trust Wallet has issued clear guidance for potentially affected users:
- Immediately disable the Chrome extension if running v2.68
- Upgrade to version 2.69 or later
- Move all funds to a brand-new wallet, as compromised mnemonic phrases can never be secured again
- Treat any wallet previously used with v2.68 as permanently unsafe
Because the attack involved private key exposure, simply reinstalling the extension is not sufficient to restore security.
Compensation and Ongoing Investigation
Trust Wallet has publicly acknowledged the breach and committed to fully compensating all affected users. A formal claims process has been launched to verify losses and distribute reimbursements.
Meanwhile, ZachXBT and other security researchers continue tracing attacker wallets and mapping fund flows, as the full scope of the compromise is still being assessed.
A Stark Reminder About Wallet Security
This incident highlights a critical risk in crypto security: supply chain attacks bypass user vigilance entirely. Even users who avoided phishing links and scams were vulnerable because the malicious code was delivered through an official distribution channel.
As browser-based wallets grow in popularity, the Trust Wallet incident underscores the need for tighter extension security, stronger key management practices, and greater transparency around software update pipelines across the crypto industry.